Cloudinary offers a cloud-based solution to help developers manage and optimize rich media (images and videos). With images being ubiquitous in online content, image sliders, which rotate banners or enable browsing through multiple images with animation effects and CSS3 transitions at the top of a website’s homepage, are becoming popular.
In our opinion, jQuery is the hands-down, No. 1 choice for building sliders. This article describes 7 ready-made, high-quality, and user-friendly jQuery sliders, complete with excellent designs and features. Also included are four tutorials along with code samples to help you build your own jQuery slider.
This is a small jQuery plugin that creates a responsive slider with the elements inside a container. It works with numerous browsers, including Internet Explorer version 6 and up. In addition, it supports `max-width` in CSS for IE6 and other browsers that don’t natively support `max-width`. You must run jQuery 1.6 and up to use this plugin. Also, keep in mind that all the images are of the same size.
Options: File links, markup, CSS, slideshow, customizable options.
License: Open Source (MIT)

This is a fully responsive, popular slider that is well supported on GitHub. The slides can contain images, video, or HTML with built-in support for touch and swipe. The file size is small and the theme, simple to implement. This slider, which uses CSS transitions for animation with native hardware acceleration, works well with Firefox, Chrome, Safari, iOS Android, and IE7+ browsers.
Options: Horizontal, vertical and fade modes, transition duration, margin between slides, starting slide, random start, slide selector, infinite loop, hiding control on end, captions, text ticker, adaptive height, animations as CSS or jQuery, preload images, swipe threshold, numbered pagination, full customization of slider controls, full callback API and public methods
License: Open Source (MIT)

Demo and Examples / Download / Documentation
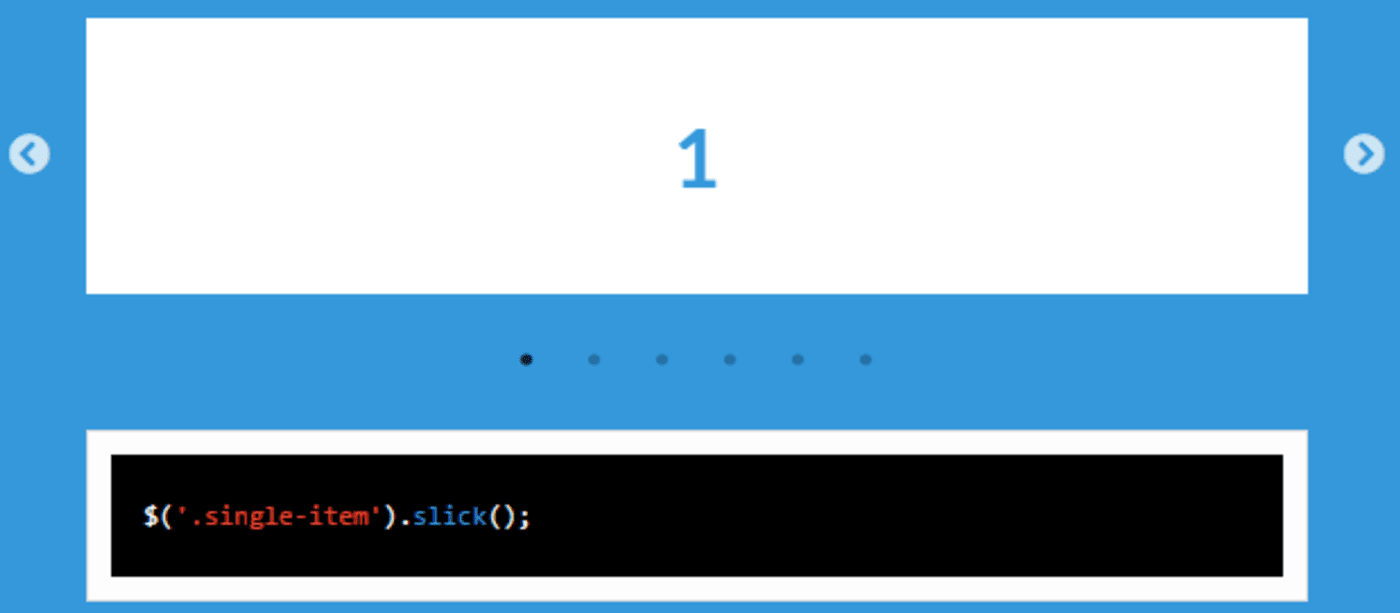
This is a fully responsive, popular slider that scales with its container and that is well supported on GitHub. Even though Slick uses CSS3 when available, it’s fully functional without CSS3. Additionally, Slick is swipe enabled with support for desktop-mouse dragging and arrow-key navigation.
Options: Separate settings per breakpoint, single and multiple items, variable width, adaptive height, lazy loading, infinite looping, add, remove, filter and unfilter slides,
autoplay, dots, arrows, callbacks
License: Open Source
This is a fully responsive slider with intuitive markup and support by all major browsers. Its features include horizontal or vertical slider and fade animations, multiple sliders, callback API, support for hardware-accelerated touch-slide, and customizable navigation options.
Options: Installation, file links, markup, animation type, easing, direction, looping, smooth height animation, slideshow and its speed and randomization, video, sliding with keyboard arrows or mousewheel, and a pause-play element
License: Open Source (MIT)
A mobile touch slider with hardware-accelerated transitions, this one is intended for use in mobile websites, mobile apps, and mobile native or hybrid apps. Swiper works with iOS, Android, and Windows Phone 8.
Options: Initialization, hash navigation, parallax, lazy loading, emitter API and events, HTML layout, CSS styles and size, and support for CDN
License: Open Source (MIT)

Demos / Download / Documentation
As its name implies, this slider is simple and small. It’s also browser friendly and responsive, with support for arrow keys, and works with all HTML content.
Options: Slideshow, order-slide display, transition, speed, show-hide navigation
License: Open Source (WTFPL)
This is a slider plugin with specific animations for each of its elements. It offers predefined animation classes and adds them to each slider element, allowing addition of classes with delay for each of the animations.
Options: Autoplay, time, animations, fade-bounce-rotate-enter left or right, delay of slide display
License: Open Source (MIT)

We collected a few great write ups from across the web showing step by step how you can easily create your own slider.

Christian Heilmann – Keeping it Simple: Coding a Carousel

Design Chemical – Lightweight jQuery Animated Slider Tutorial

We hope you enjoyed this compilation of different ways to build sliders on your site using jQuery. If you’re a user of jQuery and have additional image-related tasks on your website, or want some help preparing and optimizing the images for your slider, check out Cloudinary’s jQuery integration. We offer a very easy way to upload images, deliver them to users via CDN, and perform advanced image transformations on the fly with one line of code. If you want to try it out, sign up for our free plan.
And of course, please let us know in the comments below if you’ve tried out any of the sliders of code samples above and have any thoughts, and if you can share additional jQuery-based slider solutions.
Have a look at these articles:
- Image-Editing Basics and a Tutorial for Automation With AI
- How to Automatically Remove Photo Backgrounds in Seconds With AI
- Adding Image Watermarks, Credits, Badges and Text Overlays to Images
- Add the 360 Product Viewer to Your Commerce Site with Cloudinary
- New AI-Based Image Auto-Crop Algorithm Sticks to the Subject
- Integrating Cloudinary Into Your Shopify Store
- How to Overlay Text on Image Easily, Pixel Perfect and With No CSS/HTML
- Taking Cloudinary’s Magento Extension to the Next Level








